Ingeniero de sistemas y seguridad.Gamer en los ratos libres.Quiero compartir con todo sobre el mundo de la tecnología de manera mas fácil de entender y acercarla cada vez mas.
Zscaler Salesforce Breach Exposes Customer Support Data After Salesloft/Drift Vendor Compromise What happened Cybersecurity firm Zscaler has disclosed a data breach after threat actors gained access to its Salesforce instance and extracted customer information, including the contents of support cases. According to Zscaler’s notification and reporting by BleepingComputer, the intrusion followed compromises at third‑party vendors…
Zscaler Customer Data Exposed After Attackers Accessed Salesforce Instance Summary of the incident Cybersecurity vendor Zscaler has disclosed a data breach in which threat actors gained access to its Salesforce instance and exfiltrated customer information, including the contents of support cases. Zscaler warned customers about the incident and said the breach followed the compromise of…
Amazon disrupts Russian APT29 campaign targeting Microsoft 365 accounts Summary of the disruption Amazon has been reported to have disrupted an operation attributed to the Russian state-sponsored threat group known as Midnight Blizzard (also tracked as APT29) that sought access to Microsoft 365 accounts and tenant data. Researchers who investigated the activity described the disruption…
ScarCruft (APT37) Deploys RokRAT in “Operation HanKook Phantom” Targeting South Korean Academics Summary of the discovery Cybersecurity researchers at Seqrite Labs have identified a new phishing campaign attributed to ScarCruft, an actor widely reported as North Korea–linked and also tracked as APT37. Seqrite has codenamed the activity Operation HanKook Phantom. According to the report, the…
WhatsApp Issues Emergency Patch for CVE-2025-55177 Affecting iOS and macOS Linked‑Device Sync What happened WhatsApp issued an emergency update for its iOS and macOS clients to remediate a high‑severity vulnerability the company said may have been used in targeted zero‑day attacks. According to WhatsApp, the bug — tracked as CVE‑2025‑55177 and assigned a CVSS score…
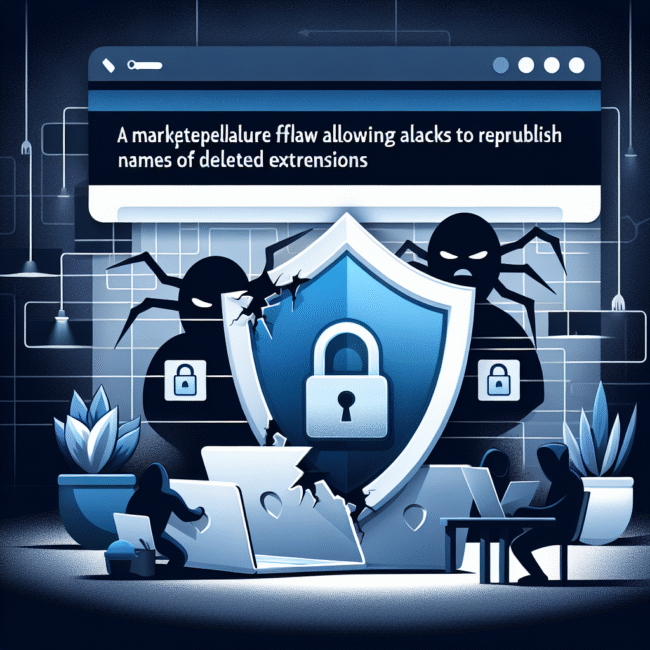
VS Code Marketplace Flaw Lets Attackers Reuse Deleted Extension Names, Researchers Warn Summary of the discovery Security researchers at ReversingLabs identified a loophole in the Visual Studio Code Marketplace that can be abused to republish extensions using the same names as previously removed packages. ReversingLabs reported the finding after it observed a malicious extension called…
VS Code Marketplace Flaw Lets Attackers Republish Names of Deleted Extensions Summary of the finding Security researchers at ReversingLabs reported a weakness in the Visual Studio Code (VS Code) Marketplace that permitted actors to reuse the names of extensions that had previously been removed. The discovery followed the identification of a malicious extension named “ahbanC.shiba”…
MathWorks breach: ransomware gang exfiltrated data on more than 10,000 people Overview of the incident MathWorks, the developer of MATLAB and Simulink, disclosed that a ransomware group breached its network in April and stole data relating to more than 10,000 people. The company reported the incident publicly after detecting the intrusion and the subsequent data…
Why Code-to-Cloud Mapping Is Becoming Essential for AppSec in 2025 The problem at a glance Picture this: developers push a change that looks harmless in a local environment but contains a subtle flaw that turns into a large-scale incident once deployed to cloud infrastructure. The vulnerability goes unnoticed until it is exploited, and the organization…
Storm-0501 Abuses Entra ID to Exfiltrate and Delete Azure Data in Hybrid Cloud Extortion Campaign Summary of the incident Recent reporting identifies a financially motivated threat actor tracked as Storm-0501 refining tactics to target hybrid cloud environments. The actor has been observed abusing Microsoft Entra ID (formerly Azure Active Directory) to gain access to Azure…