Ingeniero de sistemas y seguridad.Gamer en los ratos libres.Quiero compartir con todo sobre el mundo de la tecnología de manera mas fácil de entender y acercarla cada vez mas.
Global Campaign Unleashes TamperedChef Malware via Deceptive Software Installers Background and Context The ongoing global malware campaign known as TamperedChef underscores the growing sophistication and reach of cybercriminal activities. This campaign capitalizes on the trust users place in popular software, employing bogus installers to introduce malicious payloads onto victim machines. As digital threats evolve, such…
Thunderbird 145 Introduces Native Microsoft Exchange Support Introduction of Native Support for Microsoft Exchange On November 18, 2025, Thunderbird 145 was released, marking a significant advancement in the email client’s capabilities with the inclusion of full native support for Microsoft Exchange accounts via the Exchange Web Services (EWS) protocol. This development enables users to integrate…
Google Addresses Critical Chrome V8 Zero-Day Vulnerability with Urgent Security Update Introduction to the Vulnerability On November 18, 2025, Google announced essential security updates for its Chrome browser, targeting two vulnerabilities, including a critical zero-day flaw known as CVE-2025-13223. This particular vulnerability has a CVSS score of 8.8, indicating a significant security threat that attackers…
Google’s New Initiative to Identify Battery-Draining Android Apps Introduction In a significant move to enhance user experience and device efficiency, Google has announced that it will begin flagging Android applications in the Google Play Store that are associated with excessive background activity and battery drain. This initiative, set to commence in the coming months, aims…
Critical Vulnerability in Post SMTP Plugin Poses Risk to WordPress Sites Background and Context The Post SMTP plugin has been widely adopted by WordPress users, offering reliable and easy-to-configure SMTP mail sending options. Installed on over 400,000 WordPress sites, its integration streamlines email communications for businesses and individual users alike. However, this popularity also makes…
Immediate Response Strategies Following a Cyberattack Background: The Growing Threat of Cyberattacks The evolution of technology has, paradoxically, given rise to increasingly sophisticated cyberattacks. According to a report by Cybersecurity Ventures, cybercrime is projected to inflict damages exceeding $10.5 trillion annually by 2025. This alarming statistic highlights the urgency for individuals and organizations to recognize…
Data Breach at University of Pennsylvania Exposes 1.2 Million Donor Records Background and Context On November 2, 2025, a hacker publicly claimed responsibility for a significant data breach at the University of Pennsylvania, revealing that 1.2 million donor records were compromised. This incident highlights ongoing vulnerabilities within educational institutions, particularly regarding how they manage and…
Google’s AI Search Integration: The Future of Advertising in a New Era Introduction to AI in Search Engines The integration of artificial intelligence (AI) in search engines marks a significant evolution in how information is retrieved online. As digital landscapes become increasingly competitive, companies like Google are continually adapting to user expectations and technological advancements.…
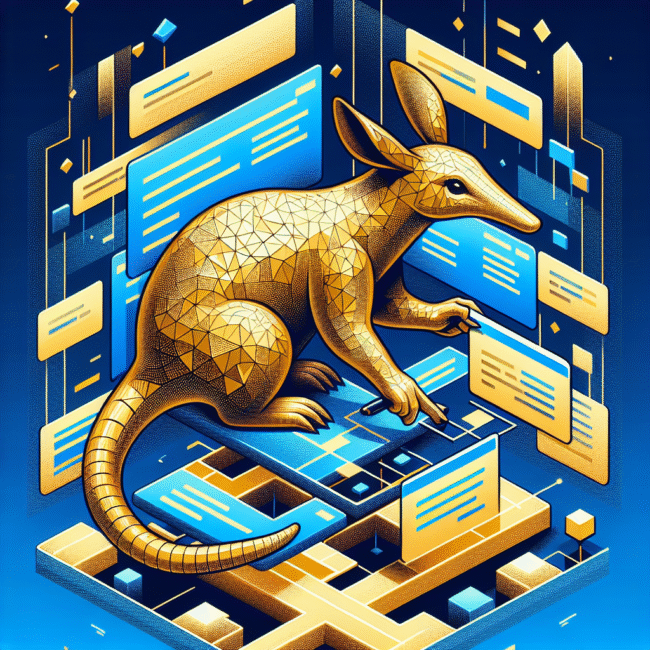
OpenAI Launches Aardvark: A Revolutionary GPT-5 Agent for Automated Code Flaw Detection and Mitigation Background and Context OpenAI, a leader in artificial intelligence research and development, has announced the launch of Aardvark, an innovative autonomous agent based on the GPT-5 architecture. This AI-driven tool is designed to perform the complex tasks of scanning, comprehending, and…
Enhancing macOS Security: Addressing Admin Errors to Mitigate Cyber Threats Background & Context In recent years, operating systems have faced increasing scrutiny regarding their security measures. As cyber threats become more sophisticated, user error remains a significant vulnerability in the overall security landscape. This is particularly relevant for macOS, where a mix of robust design…