Systems and security engineer.
Gamer in my spare time.
I want to share everything about the world of technology in a way that is easier to understand and bring it closer and closer.
In this article, we’ll see how to get password hashes from a Linux system and crack the hashes probably using the most widely used password decryption tool, John the Ripper. Requirements: Reposability: In this tutorial we will use hacking techniques, for the sole purpose of learning. We do not promote its use for profit or incorrect…
In a world where cyber threats change and evolve at practically the same speed as technology itself, security solutions are needed that not only react to the threat, but are able to anticipate it. Within those proactive solutions we have the EDR system; In this article we explain what it is, how it works and how…
SSH or Secure Shell, is a remote administration protocol that allows users to control and modify their remote servers over the Internet through an authentication mechanism. Provides a mechanism to authenticate a remote user, transfer entries from the client to the host, and retransmit the output back to the client. The service was created as…
No matter how often you connect and how or why you mainly use the Internet, you have probably seen phishing attack attempts. They are now so common and problematic that cybersecurity professionals regularly provide information to help people detect and avoid phishing attacks. Requirements: Reposability: In this tutorial we will use hacking techniques, for the…
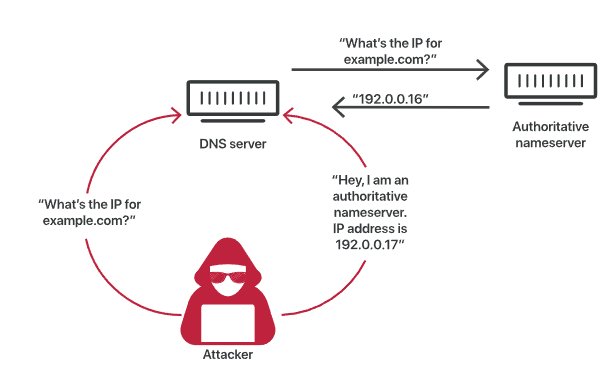
Imagine that, as a high school senior prank, the high school students change all the room numbers in the high school facilities, so that new students who don’t know the high school floor plan yet will spend the next day lost and going to the wrong classes. Now imagine that mismatched room numbers get recorded in…
As technology advances, cyberattacks are becoming more sophisticated. With the increasing use of technology in our daily lives, cybercrime is on the rise, as evidenced by the fact that cyberattacks caused 92% of all data breaches in the first quarter of 2022. Staying current with cybersecurity trends and laws is crucial to combat these threats, which can…