Systems and security engineer.
Gamer in my spare time.
I want to share everything about the world of technology in a way that is easier to understand and bring it closer and closer.
One of the cornerstones of the Internet is the Domain Name System, also known by its acronym DNS. The purpose of this protocol is to translate the domain names used by users into IP addresses that can be interpreted by machines. This protocol dates back to the 1980s, a time when functionality prevailed over security, and DNS was…
Cybercrime is an unfortunate fact of life today, regardless of whether we are talking about individual consumers or the business world in general. No company or organization is safe, and the problem is not going to get better any time soon. Experts predict that the damage caused by cybercrime will cost the world $6.1 trillion…
Clickjacking is an attack that tricks the user into clicking on a web page element that is invisible or disguised as another element. This can cause users to unintentionally download malware, visit malicious web pages, provide credentials or sensitive information, transfer money or purchase products online. Requirements: Responsibility: In this tutorial we will use hacking…
The Linux Subsystem for Windows continues to advance in capability and also in ease of use. Earlier this year, Microsoft promised an update to make it and GNU/Linux distributions easier to install, and has just implemented it in the latest Windows 10 Insider Preview Build 20246. Four years ago Microsoft announced a bombshell at its…
Imagine your website is a store, Distributed Denial of Service (DDoS) is like a mob in front of your store that won’t let your customers in. It’s a nasty situation to have tens of thousands of fake shoppers eating up your valuable resources, all at once. Know how to stop DDoS attacks. DDoS has become…
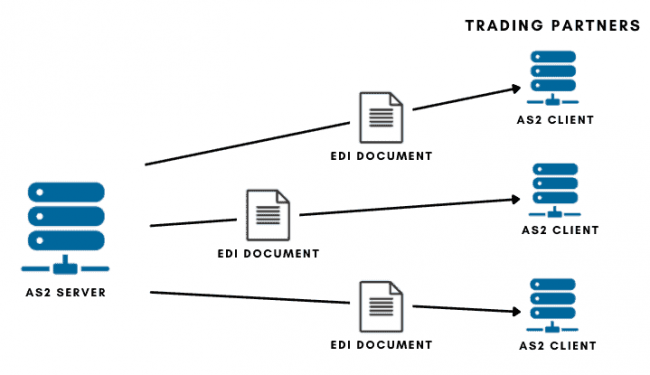
How are sensitive sectors such as commercial airlines, healthcare or transport communicated and shared data? How do you transfer structured B2B data safely and reliably through risk networks like the Internet? The answer is the AS2 protocol. What is AS2? Applicability Statement 2 ( AS2 ) is a type of file transfer mechanism based on…
What is the brute force attack method? A brute force attack uses the trial and error method to guess access information, encryption keys, or find a hidden web page. Hackers work through all possible combinations in hopes of guessing correctly. These attacks are carried out by « brute force », which means that they use…
What is SQLmap? SQLmap is a tool developed in python to automate attacks of the SQL Injection type. Its objective is to detect and take advantage of existing vulnerabilities in web applications. Once one or more possible injections have been detected, the user has the possibility to choose from a variety of options, such as listing…
¿What is the persistent back door? As we know that persistence is also known as permanent. Persistent back doors help us have permanent access to the system. There are many types of persistent rear doors but they work similarly. Usually, the attacker create a backdoor service with the help of metasolpit frame and load in…
Preamble In a fast-paced and ever-changing world of cybercrime threats, the tenacity and adaptability of malicious actors is a significant concern. BLISTER, a malware loader initially discovered by Elastic Security Labs in 2021 and associated with financially-motivated intrusions, is a testament to this trend as it continues to develop additional capabilities. Two years after its initial discovery,…