Imagine your website is a store, Distributed Denial of Service (DDoS) is like a mob in front of your store that won’t let your customers in. It’s a nasty situation to have tens of thousands of fake shoppers eating up your valuable resources, all at once. Know how to stop DDoS attacks.
DDoS has become a major problem for businesses around the world. Hackers use this attack by overwhelming traffic and victimizing critical web resources, ultimately making the server unavailable to satisfy genuine requests. Bot-for-hire services, which offer bogus traffic for as little as $5 an hour, put virtually every business at risk of attack.
Check out some recent findings that provide insight into the lethality of a DDoS attack.
- DDoS attacks cost banks up to $100,000 per hour.
- Twenty percent of these attacks last for days or even months.
- 87% of the attacked companies were hit more than once.
No matter what business you’re in, keeping a business application up and running is critical to your brand’s reputation, and hackers want to exploit this weakness with DDoS attacks. The unpredictability of these attacks makes it difficult to prepare for them, which further incentivizes criminals to take action.
Let’s learn more about the problem and how your company and data centers can defend against DDoS attacks.
What are the types of DDoS attacks?
1 – Volume-based DDoS attacks
This is a classic type of DDoS attack, which exerts a massive amount of traffic to saturate bandwidth and makes it impossible for valid traffic to flow in and out of the victim’s site. Attackers carry out this volumetric DDoS attack to completely saturate the target’s network capacity.
2 – Protocol-based attacks
This type of DDoS attacks are built to consume the processing capacity of network resources such as firewalls, servers and load balancers by targeting layer 3 and 4 protocol communications with malicious connection requests. In this attack, packets are created to make communicating servers expect a non-existent response during a normal protocol handshake.
3 – Application-based attacks
Most sophisticated attacks involve exploiting vulnerabilities in the application layer – Layer 7. There is no exception for DDoS attack as well. In these types of DDoS attacks, hackers use weaknesses in the application software or web server software, which causes the server to crash or hang. The most standard type of application DDoS attack involves initiating partial requests to a server to consume finite resources and make the entire database connection pool busy so that it can bottleneck legitimate requests.
There are broad subtypes of attacks, which fall into any of these common types of DDoS protection but exhibit unique characteristics. Some of the most popular DDoS attack methods are:
- SYN Flood
- SYN-ACK Flood
- LAND attack
- ACK & PUSH ACK Flood
- Fragmented ACK Flood
- Spoofed Session Flood (Fake Session Attack)
- UDP Flood
- VoIP Flood
- DNS Flood
- NTP Flood (NTP Amplification)
- SSDP Flood
- SNMP Flood (SNMP Amplification)
- CHARGEN Flood
- Misused Application Attack
- ICMP Flood
- Smurf Attack
- Slowloris
- Zero-Day DDoS
How to prevent DDoS attacks?
Step 1: Understanding that every company is vulnerable
The first line of defense in DDoS protection is to understand how vulnerable your business is.
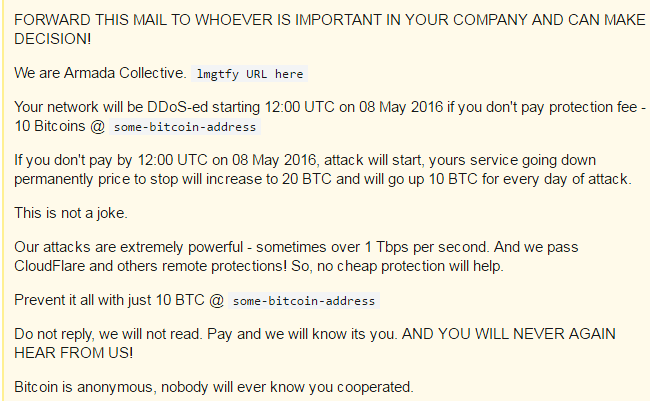
While many DDoS attacks are motivated by revenge, politics, trolling and terrorism, money is often involved. According to cybersecurity analysts, ransom and blackmail are the most common motives behind DDoS attacks. Hackers disrupt web services and demand a ransom. Hackers ask for hefty ransom amounts, which when paid, cause the attack to stop and services to be made available to customers.
Similarly, competition motivates people to take down better-performing rivals, while revenge by disgruntled employees has a similar impact. Politics, terrorism, war and distraction techniques masking other hacking attempts are also common reasons for carrying out DDoS attacks on applications.
Primary attack motivation:

Step 2: Deploy protection tools
Network DDoS: Network-level DDoS attacks attempt to exploit the network by sending more data packets than a server can handle, or by abusing bandwidth beyond the capacity of the network port. They are often featured in the media because of their record volume.
Application DDoS: On the other hand, application layer attacks are quieter and lower volume, but cause much more damage. As most enterprises deploy their resources in the cloud, hackers are now exploring attack options beyond the network layer.
“These attacks are also more frequent due to lower resource requirements. For example, an application on Amazon Web Services (AWS) can process a SYN flood of up to 200,000 packets (“elastic bandwidth costs” is an entirely different discussion). However, the same AWS server instance can be brought down by a meager 500 HTTP requests per second when the application is running on CMS (Joomla or WordPress).”
See the difference? 500 HTTP requests per second is a cheaper attack to execute.
More sophisticated Layer 7 DDoS attacks not only take down the server, but also aid in data breaches. In one such attack, California State University, Sacramento lost 1,800 Social Security and driver’s license numbers of its staff. The attackers used multiple compromised systems to spoof the DNS server and leak the authentication security code.
WAF deployment is one of the best methods of preventing DDoS attacks.

Step 3: Continuously monitor application traffic
Nothing can prepare your company to detect and prevent DDoS attacks better than continuous monitoring. Security experts can distinguish sudden spikes in traffic from bot traffic. Ultimately, this monitoring provides actionable data on attack vectors to define DDoS protection policies.
A distributed denial-of-service attack at the application layer is initiated by hiring machines, bots, or taking control of remote systems. These components are used to generate fake requests to a target server. With this large number of fake requests, cybercriminals attempt to make the services of an application or server unavailable for hours, days or weeks. A successful DDoS attack can consume huge chunks of bandwidth, processing speed and memory to slow down and/or disrupt applications.
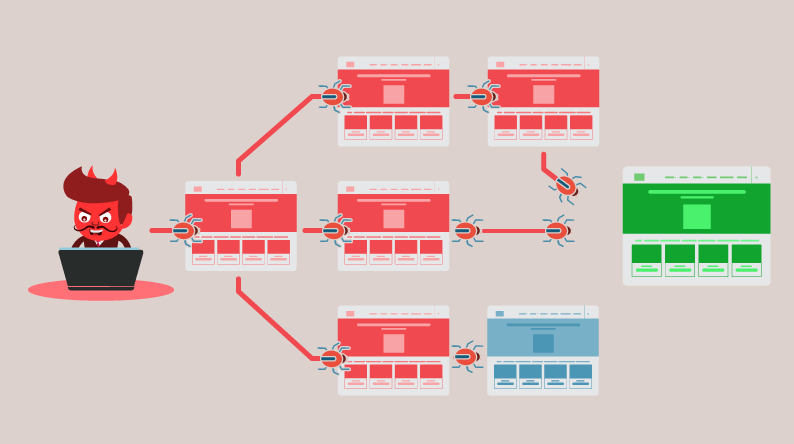
The ease of availability makes a DDoS attack at the application layer more lethal than a similar attack at the network layer. Anyone can buy the custom-coded DDoS module and launch it on any desired web application. In fact, with a little knowledge of the underground markets, a basic DDoS attack will not cost the perpetrator more than a few hundred dollars. Although there are different types of sophisticated DDoS attacks, this is the most common.
Compared to network-layer DDoS, application DDoS is much easier to execute. It requires less computing power and fewer systems, which still leads to catastrophic results (one of the main reasons why application DDoS is becoming more and more prevalent).
Take the Slowloris attack as an example. Slowloris was originally created to show how a single machine could keep multiple connections open simultaneously for long periods of time, eventually crashing the server. Slowloris has become more sophisticated over time, and it still only takes a few machines (generating several thousand requests each) to cause a server to run out of connection pools and crash, making it a major threat.
Step 4: Internal DDoS or managed application security
You can hire and train experienced Layer 7 security professionals to stop DDoS attacks and other application security risks internally. A dedicated team can monitor attacks and take action efficiently.
However, due to the shortage of experienced cybersecurity manpower and the huge costs involved in hiring and managing these teams, startups invest in managed application security providers to stop DDoS attacks. Such a team not only provides 24 × 7 traffic monitoring and DDoS attack mitigation, but comprehensive application security that includes:
- Latest security notification to protect your applications from known vulnerabilities.
- Periodic penetration tests.
- Business logic testing on all applications to find vulnerabilities, zero-day threats and automated application risks.
- Customized WAF rules to block attacks (via virtual patches).
- Tracking an attacker’s malicious behavior initially versus simply blocking the attack.
- 24/7 monitoring to collect information such as IP address, user ID if authenticated, GEO location, browsing/user behavior and machine fingerprinting that can help gain insight into the attacker’s methodologies to use that information to create more aggressive blocking rules for these attackers.
Conclusion
DDoS attacks will always exist and will always be more complex, the best thing is to have our company well updated with the best tools and market trends. And remember that the weakest link is us, the humans.
I hope you find this post helpful.







