Emergence of a New TrickMo Variant: Exploiting TON C2 and SOCKS5 for Android Network Attacks
Introduction to TrickMo
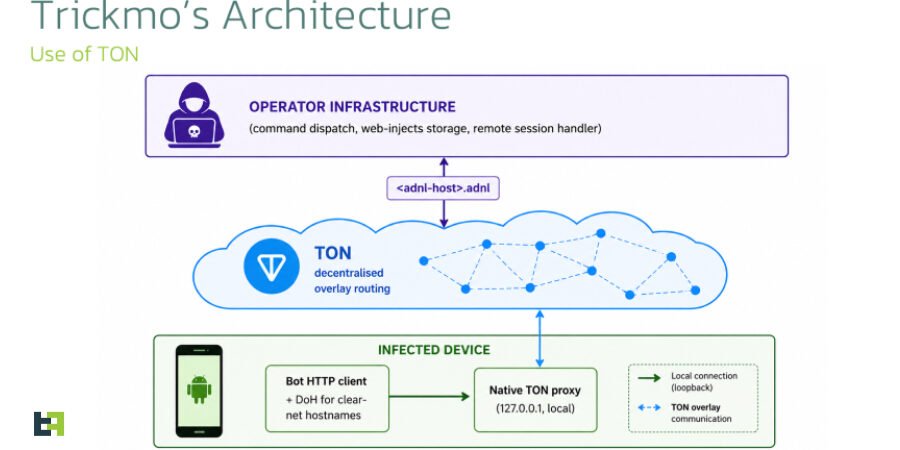
The TrickMo banking trojan has evolved yet again with the introduction of a new variant that utilizes The Open Network (TON) for its command-and-control (C2) operations. This development has raised alarms among cybersecurity experts, especially as the trojan intensifies its focus on banking and cryptocurrency wallet users across Europe.
Characteristics of the New TrickMo Variant
Discovered by cybersecurity firm ThreatFabric between January and February 2026, this new TrickMo variant showcases a sophisticated method for maintaining persistent network connections. Key features include:
- Utilization of TON for command-and-control communications.
- Employment of SOCKS5 proxies to facilitate seamless network pivots.
- Runtime-loaded APK (dex.module) that enhances its stealth and evasion techniques.
Target Demographics: Banking and Cryptocurrency Users
The new TrickMo variant primarily targets individuals in France, Italy, and Austria, focusing on those with banking and cryptocurrency wallets. This strategic targeting raises significant concerns regarding the financial security of users in these regions.
- Increased phishing attempts targeting online banking credentials.
- Attempts to gain unauthorized access to cryptocurrency wallets for financial theft.
- Exploitative techniques to inject malicious code through socially engineered downloads.
Technical Analysis of the Trojan’s Functionality
Cybersecurity experts have noted that this iteration of TrickMo is particularly adept at remaining undetected. By leveraging the capabilities of TON and SOCKS5, the trojan can obscure its origin and communications. The technical implications are significant:
- TON Usage: The Open Network framework provides a decentralized approach to C2 operations, potentially complicating efforts to track and mitigate the threat.
- SOCKS5 Proxy Integration: This allows attackers to route traffic through a series of servers, making it difficult for security tools to intercept communications and identify the trojan’s activity.
- Dynamic APK Loading: The use of runtime-loaded APK files enables TrickMo to adapt dynamically, downloading additional payloads or updates as needed, thereby enhancing its resilience against detection.
Implications for Cybersecurity Landscape
The emergence of this new TrickMo variant underscores a worrying trend in the cybersecurity landscape, particularly in relation to banking and financial institutions. The implications can be profound:
- Increased focus on securing mobile banking applications against sophisticated malware.
- Potential for regulatory changes as financial institutions seek to protect customers from such threats.
- Collaboration between countries may be needed to address the transnational nature of cybercrime enabled by decentralized networks.
Conclusion
The new TrickMo variant’s use of TON and SOCKS5 proxies marks a significant development in the tactics employed by banking trojans. As this threat continues to evolve, it is crucial for users to remain vigilant and for security professionals to fortify defenses against such sophisticated attacks. Ongoing awareness and education will be essential in combating these risks in the financial sector.
Source: thehackernews.com