Emerging Threat: PamDOORa Backdoor Leverages PAM Modules for SSH Credential Theft
Background and Context
The cybersecurity landscape is perpetually evolving, with new threats emerging at an alarming rate. Among the most concerning are backdoors—a type of malware that provides unauthorized access to systems while often remaining undetected. The recent revelation of a backdoor named PamDOORa, which exploits Pluggable Authentication Modules (PAM) on Linux systems, exemplifies this trend. Advertised on a Russian cybercrime forum for $1,600, this tool not only highlights the sophistication of current threats but also underscores the growing commodification of hacking tools in underground markets. For administrators and security teams alike, the implications are profound, as such backdoors can lead to significant data breaches, financial losses, and a general erosion of trust in digital systems.
Historically, Linux systems have been perceived as more secure than their Windows counterparts, primarily due to their open-source nature and the smaller attack surface they present. However, incidents like the compromise of the SolarWinds supply chain and the exploitation of vulnerabilities in widely used software libraries have shown that no system is immune to targeted attacks. The emergence of PamDOORa serves as a reminder that as the Linux ecosystem grows, so too does its appeal to threat actors. With the shift to remote work and the increasing reliance on cloud infrastructures, the stakes have never been higher. The potential for backdoors to facilitate persistent access to systems raises the bar for cybersecurity defenses and necessitates a reevaluation of existing security protocols.
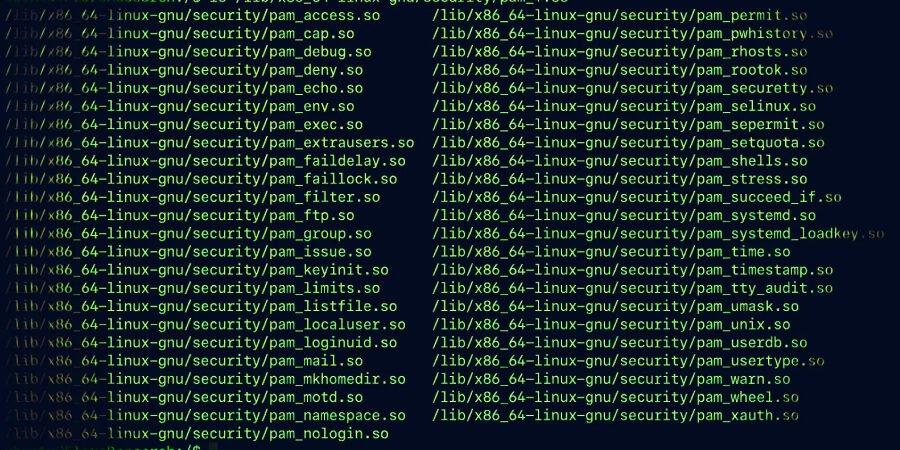
Moreover, the use of PAM as an attack vector is particularly alarming because it leverages a legitimate system feature to gain unauthorized access. PAM modules are integral to the authentication process on Linux systems, allowing for flexible management of authentication tasks. Consequently, a backdoor that operates within this framework can evade traditional detection mechanisms, making it both insidious and difficult to remediate. This incident highlights the urgent need for organizations to enhance their security postures and develop a more robust understanding of PAM and its potential vulnerabilities.
Technical Analysis
PamDOORa operates by integrating itself into the PAM framework, which is a critical component of Linux security architecture. By doing so, it can manipulate the authentication process, thereby allowing unauthorized users to gain access to systems through SSH without raising alarms. The backdoor uses a combination of a “magic password” and specific TCP port settings to establish a foothold in compromised systems. This method not only ensures persistence but also complicates detection efforts.
To understand the technical workings of PamDOORa, it’s essential to consider several core components:
- Modular Architecture: PAM’s design allows for the inclusion of third-party modules, which can be exploited to insert malicious code without altering the core system files. This flexibility is what makes PamDOORa particularly dangerous.
- Stealth and Evasion: The backdoor’s integration into the authentication process allows it to function in the background, effectively bypassing traditional monitoring tools that might flag unusual behavior.
- Remote Access Capabilities: By establishing SSH access, the backdoor enables attackers to control compromised systems remotely, facilitating further attacks or data exfiltration.
The implications of such a backdoor extend beyond mere access; they can lead to extensive data breaches, the deployment of ransomware, or the establishment of botnets for larger-scale attacks. As evidenced by prior incidents involving similar exploitation of legitimate tools, such as the use of PowerShell in Windows environments, the risks associated with PamDOORa are profound and far-reaching.
Scope and Real-World Impact
The potential scale of impact from the PamDOORa backdoor is significant, affecting potentially thousands of organizations worldwide that rely on Linux servers for critical operations. Given the growing adoption of Linux in enterprise environments, especially in cloud computing and server management, the risk is not confined to any single sector. According to estimates, over 70% of public cloud workloads run on Linux, which means a backdoor like PamDOORa could pose a threat to various industries, including finance, healthcare, and technology.
Comparatively, past incidents such as the exploitation of the OpenSSL Heartbleed vulnerability or the Shellshock bug in Bash highlight how a single vulnerability can lead to widespread consequences. Both incidents resulted in millions of systems being compromised or at risk, leading to extensive remediation efforts and financial fallout. Similarly, the emergence of PamDOORa could lead to significant operational disruptions and financial losses as organizations scramble to defend against an attack that leverages a core component of their security framework.
Furthermore, the commodification of such sophisticated backdoors in underground markets indicates a troubling trend. As cybercrime becomes increasingly lucrative and accessible, even less skilled threat actors may gain the ability to deploy advanced attacks, further exacerbating the challenges faced by cybersecurity professionals.
Attack Vectors and Methodology
The operational methodology of the PamDOORa backdoor unfolds in several critical steps, illustrating the complexity and sophistication of modern cyber threats:
- Initial Compromise: Attackers may gain initial access through phishing, exploiting vulnerabilities, or leveraging stolen credentials.
- PAM Module Insertion: Once access is secured, the attackers deploy the PamDOORa backdoor by inserting malicious PAM modules into the Linux authentication framework.
- Configuration of Access: The backdoor is configured with a “magic password” and specific TCP port settings to enable persistent SSH access.
- Stealth Operation: The backdoor operates undetected, allowing attackers to maintain a foothold in the system for extended periods.
- Data Exfiltration or Further Compromise: With continued access, attackers can either exfiltrate sensitive data or deploy additional payloads for broader attacks.
This multi-step methodology underscores the importance of understanding both the technical aspects of such backdoors and the strategic approaches employed by attackers.
Mitigation and Defense Recommendations
To defend against threats like PamDOORa, organizations must adopt a multi-layered security strategy. Here are several actionable recommendations for both system administrators and end-users:
- Regular Security Audits: Conduct routine audits of PAM configurations and access logs to identify unauthorized changes or anomalies.
- Implement Least Privilege: Limit access rights to only those users and processes that require them, minimizing the risk of exploitation.
- Monitor Authentication Activities: Utilize intrusion detection systems (IDS) to monitor and alert on suspicious authentication activities.
- Patch and Update Systems: Regularly update all software, including PAM modules, to mitigate the risk of exploitation through known vulnerabilities.
- Educate Employees: Train staff on recognizing phishing attempts and other social engineering tactics that could lead to initial compromises.
By implementing these measures, organizations can bolster their defenses against backdoors like PamDOORa and other emerging threats.
Industry Implications and Expert Perspective
The rise of the PamDOORa backdoor reflects broader trends in the cybersecurity landscape, where threat actors are becoming increasingly sophisticated and organized. The commodification of hacking tools, as evidenced by their availability on cybercrime forums, signals an alarming shift that could democratize access to advanced cyber capabilities. This trend not only poses challenges for individual organizations but also raises concerns about national security, especially as state-sponsored actors may leverage similar tools for espionage or disruption.
Experts emphasize that the emergence of such threats necessitates a reevaluation of existing security frameworks. Organizations must adopt a proactive approach to cybersecurity, focusing not only on prevention but also on detection and response strategies. Moreover, the incident underscores the need for greater collaboration among cybersecurity professionals, government agencies, and the private sector to share threat intelligence and best practices.
Ultimately, the PamDOORa backdoor serves as a stark reminder of the evolving nature of cyber threats and the importance of vigilance in an increasingly interconnected digital landscape.
Conclusion
In conclusion, the emergence of the PamDOORa backdoor highlights the complexities and challenges faced by the cybersecurity community in safeguarding Linux systems. With its ability to exploit legitimate PAM modules, this backdoor exemplifies the innovative tactics employed by modern threat actors and the potential for widespread damage. As organizations continue to adapt to a rapidly changing digital environment, the need for comprehensive security strategies has never been more critical.
The lessons drawn from this incident, alongside its implications for future cybersecurity trends, should serve as a clarion call for organizations to bolster their defenses and remain vigilant against the ever-evolving threat landscape. As the line between legitimate and malicious code becomes increasingly blurred, the need for robust authentication and monitoring mechanisms will be paramount in securing our digital infrastructure.
Original source: thehackernews.com